99% secure is a 100% unsecure
Make Your Cloud Impenetrable
with
Security Audit
Performance Optimizer
Fault Tolerance
Service Limits
Check out the potential of Security and Health in less than 100 seconds
Cloud Security is a shared responsibility between you, the cloud providers and Centilytics. You are an expert on your application,
hence best-fitted to secure from the Operating System (OS) to the Application layer. Cloud providers are experts in securing from the Physical (Bare Metal) to the Hypervisor layer.
Centilytics is an expert on what's left in the middle i.e. Hypervisor to Operating System (OS) layer.
Your dynamic cloud infrastructure can fall vulnerable to 400+ points of failures. Be it fault tolerance, performance optimization, service limits breaches, or security loopholes;
Centilytics' Security and Health can identify all those vulnerabilities in your infrastructure within a single pane of glass.
Get a turnkey solution tailored to manage all the compliances such as PCI, CIS, HIPAA, GDPR, ISO 27001, CSA and NIST 800-53.
The severities, categorized as Critical, Warning and OK, help you prioritize which issues need to be
tackled first.
Solutions
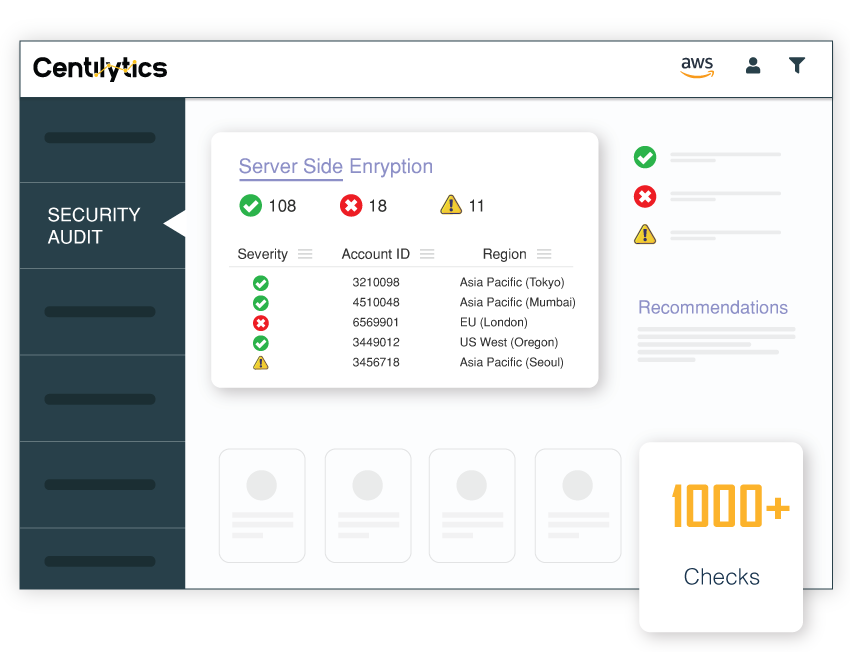
Security Audit
Security audit helps you identify loopholes, asses risks, and remediate the vulnerabilities that exists in your multi-cloud.
Get enhanced compliance management and follow industry 'best practices'
for your unique infrastructure.
Highlights
- Security overview on a single pane of glass
- 300+ Service-wise security checks
- One-click fixes
- Compliances managed: GDPR, HIPPA, PCI, NIST, ISO, CSA, CIS, Trusted Advisor, Azure Advisor

Performance Optimizer
Inefficient use of resources may lead to performance degradation. Get dedicated checks to track overutilized instances and ensure that your applications make the most out of provisioned resources to improve overall performance.
Fault Tolerance
Organizations handling critical data in cloud never want to experience downtime leading to business losses. Security and Health provides disaster recovery readiness with fault tolreance insights such as AMI age, snapshot age, backups etc.

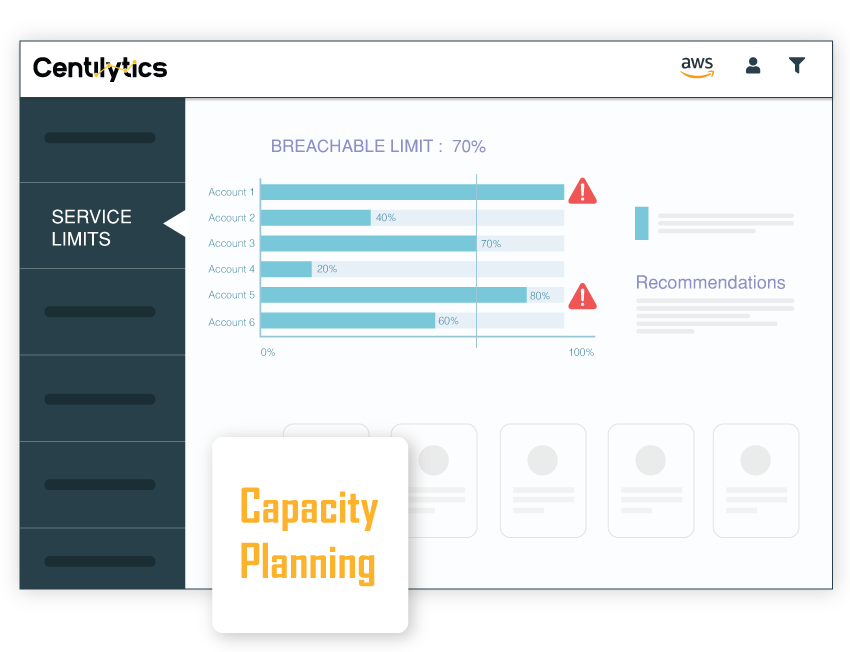
Service Limits
Public cloud providers define a limit to each service which you can further increase depending
on whether it is a soft limit or hard limit. Breaching these limits can cause failure of required actions
and prevents scalability of your infrastructure. Now, track and perfectly manage service limits with
actionable insights and warnings.
Overview Dashboard
Quickly understand the security posture of your infrastructure with simplified graphical representations based on various severities.
Multi-account & Multi-cloud view
Easily navigate through multiple accounts and multiple clouds within a single pane of glass, and identify the security loopholes in your infrastructure.
Filters
Get a multi-faceted view to look at your infrastructure's security from different angles with powerful filters based on regions, compliances etc.

0 +
Health Checks

0 +
Security Checks

0 +
Service Limits
Who is it for?
Office of the CIO
Tackle all the vulnerabilities of your infrastructure with one-click fixes and ensure business continuity with proven disaster recovery strategies.
See how we can help CIOsOffice of the CTO
Get the ability to pin-point the exact loophole leading to an exposed infrastructure and implement security best practices cross your multi-cloud.
See how we can help CTOsInfra & Ops
Implement end-to-end security by tracking all the weaklinks, identify opportunities to optimize resources for better performance and practice disaster recovery strategies.
See how we can help CFOsSecurity and Ops
Identify security loopholes, get one-click fixes and implement disaster recovery strategies to ensure business continuity and no downtime in business operations.
See how we can help SecurityCustomer Stories
"...provides valuable insights into our AWS infrastructure..."

Anirban Mandal
Deputy Director – Technology | NASSCOM
"...cost-effective way to gain granular visibility into our infra..."

Parthasarathy S
Global Infrastructure Lead | LRN
"...cloud billing through Centilytics was a seamless process and..."






